The Moving Target: Open Source Release of Phoenix
Why Your Kubernetes Security is a Sitting Duck and You Have No More Excuses
Security people love a metaphor. Usually, it’s a castle. Thick walls, deep moats, and some poor sod in a suit of armor standing at the gate pretending he’s not freezing his bollocks off. In the digital world, we call that “detection.” You sit there, you wait for a light to blink red, and then you scramble.
It’s rubbish. It’s reactive. It’s like waiting for a burglar to finish his tea in your kitchen before you decide to check if the front door was locked.
Then there’s deception. Honeypots. Leaving a fake wallet on the table while you hide in the pantry. It’s a nice trick, sure. It might distract a particularly dim-witted intruder for five minutes. But while they’re poking at your fake wallet, your actual house is still standing exactly where it was when they checked Google Maps. Deception is just a polite way of lying to someone who’s already in your hallway. Deception isn’t enough because it doesn’t solve the fundamental problem: your real infrastructure is still a stationary target.
That’s why we’ve finally pulled the trigger and put Phoenix into the wild. It’s an open-source Kubernetes operator, and it doesn’t bother with the parlor tricks.
The Art of Not Being There
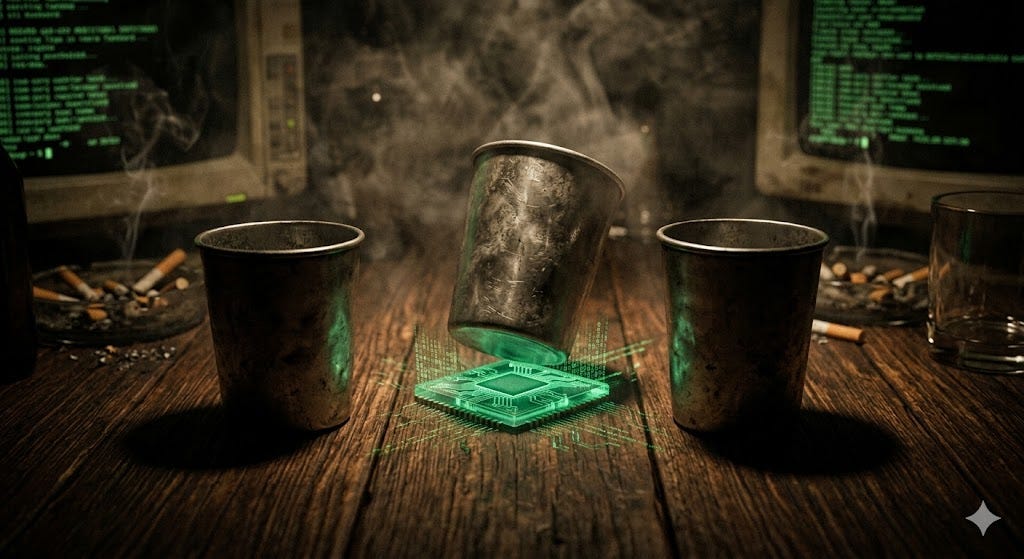
Phoenix is based on Automated Moving Target Defense (AMTD). If you want a metaphor that actually works, stop thinking about castles and start thinking about a shell game. By the time the attacker works out where the data is, Phoenix has already moved the pods, rotated the identities, and scrubbed the floor.
It’s proactive. It’s low-touch. It’s “no-nonsense” security for people who have better things to do than chase Falco alerts all night. We’re opening the source because, frankly, the more people using it, the more annoyed the bad guys get. And making people annoyed is one of the few things I still find professional satisfaction in.
What’s in the Box (And What Isn’t)
The open-source version is the base layer. It’s enough to level up your defenses significantly because it fundamentally changes the physics of the attack. It doesn’t care if a zero-day exploit exists; it just makes sure the target isn’t there long enough for the exploit to matter.
It’s the digital equivalent of moving the office every time a debt collector finds the address.
Now, for those of you with bigger budgets and more ego - the ones running “AI workloads” and Nvidia NIM stacks - we have a closed-source version. That’s where the real heavy lifting happens. What’s missing from the repo?
More complex, granular policies for those of you with too many compliance officers.
Specialized AI workload support (especially for those of you babysitting Nvidia NIM nodes).
Advanced predictive logic that makes decisions faster than a bored civil servant.
Collaboration between distributed teams and agents
But for the rest of you? Start with the open-source operator. Stop being a sitting duck.
Because in this game, if you aren’t moving, you’re already dead. You just haven’t fallen over yet.
Check the repo here: https://github.com/r6security/phoenix