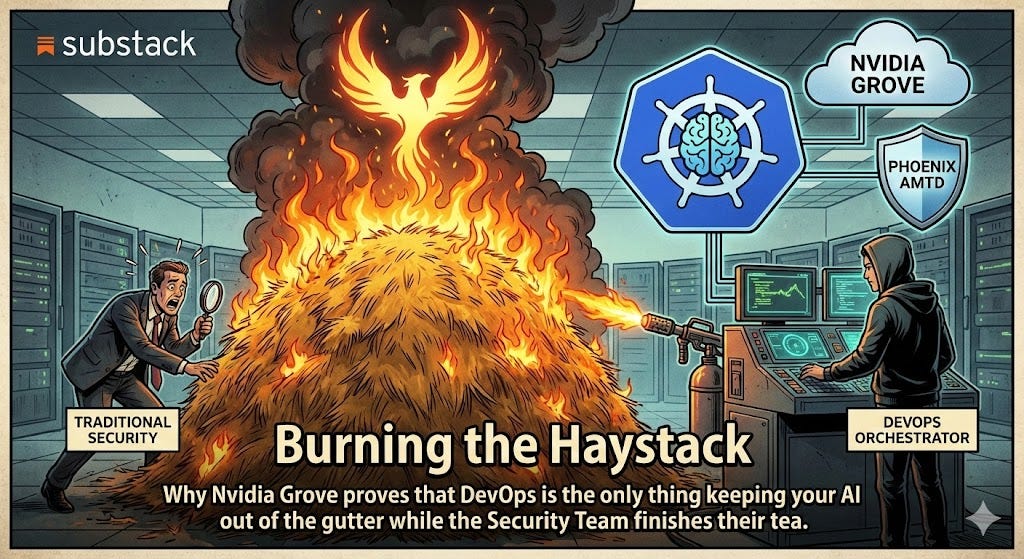
Burning the Haystack
Why Nvidia Grove proves that DevOps is the only thing keeping your AI out of the gutter while the Security Team finishes their tea
When the Infrastructure Shambles
Listen, the problem with most “security” in this industry is that it’s handled by people who think a firewall is a personality trait. They love a perimeter. They want to build a big, static wall around your AI cluster, sit back with a spreadsheet, and pretend they’ve done a day’s work.
In the real world - especially in 2026 - static is just another word for “dead.” If your LLM pods are sitting there for three weeks, some script kiddie in a basement has already mapped your memory, found your secrets, and is currently using your GPUs to mine whatever the latest sh1tcoin is.
Traditional security teams are reactive. They wait for a red light to blink, then they spend four days arguing about who’s supposed to fix it. If you want actual security, you don’t look to the people with the clipboards; you look to the people who control the orchestrator. Because in the AI era, orchestration is the only security that works.
Nvidia Grove: The Adult in the Room
Kubernetes, by itself, is “AI-blind.” It treats a complex, multi-node inference stack like it’s a collection of isolated web servers. It has no idea that if the “Leader” pod dies, the “Worker” pods are just expensive space heaters.
Nvidia Grove fixes this by giving K8s a brain. It uses something called a PodCliqueSet. It’s not just a fancy name; it’s a hierarchical blueprint that treats your entire AI stack - prefill, decode, routing - as a single, logical system.
Explicit Startup Ordering: Grove ensures the components start in the right order. No more deadlocks or “zombie” pods waiting for a scheduler that hasn’t booted yet.
Topology Awareness: It knows exactly where the GPUs are and how they’re wired. It packs the pods together so they aren’t shouting across the data center through a straw.
When you use Grove, you aren’t just deploying code; you are defining the architectural intent. And once you have that level of control, you can start doing the clever stuff with Phoenix.
Phoenix AMTD: The Moving Target
Now, let’s talk about Phoenix AMTD (Automated Moving Target Defense). If Grove is the map, Phoenix is the shell game.
Most security tries to “detect” an intruder. It’s a loser’s game. Phoenix doesn’t care if someone is in the system because, by the time the attacker has found their bearings, the system has already been destroyed and rebuilt.
Continuous Container Rotation: Phoenix takes the ephemeral nature of Kubernetes and puts it on steroids. It automatically rotates and refreshes your containers, nodes, and resources.
Zero Trust via Ephemerality: Because the environment is constantly “burning down” and respawning in a slightly mutated state, an attacker can’t achieve persistence. There is no floor for them to stand on.
The DevOps Link: This is why it beats a traditional security team. Phoenix isn’t a “bolt-on” dashboard. It’s a K8s Operator. It lives in the same YAML files that the DevOps team uses to scale the cluster.
If you’re running a massive AI agentic pipeline, you can’t have a human security analyst checking every new endpoint. You need the orchestrator to bake “rotation” into the lifecycle of the pod.
Why the Orchestrator Wins
The “Security Team” wants to patch servers. The “DevOps Team” just kills them.
In a Grove-managed cluster with Phoenix AMTD running, the DevOps team is the most effective security force in the building. Why? Because they operate at the infrastructure level.
The Orchestration Paradox
The fundamental difference between a traditional security team and a Grove-powered DevOps unit isn’t just tools—it’s philosophy. While the “Suits” are busy trying to patch an infected container like they’re performing surgery on a corpse, the DevOps orchestrator has already killed the pod and spawned a fresh one. Traditional security is static; it builds a wall and waits for it to be breached. DevOps-led orchestration is dynamic; it uses Phoenix AMTD to mutate the attack surface so fast that the “wall” has moved before the attacker can even find the door. By baking security directly into the YAML scaling policies, you move from a reactive stance (waiting for the alert) to a preemptive one (burning the haystack every ten minutes). In short: the Security Team wants a report; the DevOps Team wants a moving target.
By the time the Security Team has finished drafting a memo about a new vulnerability, the DevOps team’s orchestrator has already rotated the entire cluster five times, effectively making the vulnerability irrelevant.
The Bottom Line
Stop listening to people who talk about “securing the perimeter.” In 2026, there is no perimeter. There is only the orchestrator and the attacker.
If you use Nvidia Grove to define exactly how your AI should behave, and Phoenix AMTD to ensure that environment never stays the same for more than ten minutes, you haven’t just “improved” your security. You’ve made it a side effect of being competent.
Security teams look for a needle in a haystack. DevOps just burns the haystack every morning and builds a new one. I know which one I’d put my money on. Now, get back to your office and go check your YAML.
And sign up if you want to actually know how to run a cluster without becoming a headline. Or don't, and keep filling out those "Risk Assessment" spreadsheets.
Before the haystack burns down again.


Excellent analysis, this really builds on your previous thoughts on proactve AI security. Do you think we'll see native AI-aware K8s features eventually?